Posted: March 7th, 2016 | Author: xanda | Filed under: IT Related | Tags: IOC, Locky, Ransomware | No Comments »
While “Locky” is still hot. Let me write a small update on my findings.
Based on the (new) DGA algorithm published in Forcepoint’s blog post, with the help of pyLockyDGA project, I’ve performed a minor patch on the python code to allow me to automate some stuff.
I quick run for 1 month DGA lead me to the following results (filtered to see only registered and resolved domains):
qxicsfgofp.in
yqbcarhmtuskpq.be
taflicbfuos.pw
yqbcarhmtuskpq.be
taflicbfuos.pw
afcnikg.be |
qxicsfgofp.in
yqbcarhmtuskpq.be
taflicbfuos.pw
yqbcarhmtuskpq.be
taflicbfuos.pw
afcnikg.be
Whois record all of those domains contains these 2 emails
- jgou.veia@gmail.com
- tech1@101domain.com
And from a quick search, jgou.veia@gmail.com is a known threat actor involved with several botnet CnC domains earlier and also mentioned several legal notices. I also found a few domains registered by tech1@101domain.com has been sinkholed by several law enforcement and regulators. With those findings, i simply conclude that those emails can be (potentially) associated directly or indirectly with Locky. (unless they are security researchers who registered the domains for sinkhole/research purpose)
IP resolved by those domains in the list above are:
- 195.22.28.196
- 195.22.28.197
- 195.22.28.198
- 195.22.28.199
Thanks to whoxy.com ; domains registered by jgou.veia@gmail.com can be found here [compact whois record] and domains registered by tech1@101domain.com can be found here [compact whois record]
Copy and paste version of the IOCs is available here
Any error or mislead information? Please let me know by email or in the comment. Thanks 🙂
Posted: January 25th, 2016 | Author: xanda | Filed under: IT Related | Tags: APT, IOC | No Comments »
[Quick and short update]
Last couple of weeks, I was reading the The EPS Awakens – Part 2 blog entry from FireEye and found this one IP, 121.127.249.74, was previously used as their C2 server. I used VirusTotal IP information, these few domains appeared:
2015-07-01 frppl.com
2015-07-01 jrjfj.com
2015-07-01 pjntx.com
2015-07-01 vzflx.com
2015-07-01 yeaqm.com |
2015-07-01 frppl.com
2015-07-01 jrjfj.com
2015-07-01 pjntx.com
2015-07-01 vzflx.com
2015-07-01 yeaqm.com
I went and check more information on each domain listed and found new infra (IPs) being used:
frppl.com domain information
2015-12-21 123.60.73.10
2015-07-01 121.127.249.74
jrjfj.com domain information
2015-12-21 123.60.73.8
2015-07-01 121.127.249.74
pjntx.com domain information
2015-12-28 123.60.73.9
2015-07-01 121.127.249.74
yeaqm.com domain information
2015-12-27 123.60.73.6
2015-07-01 121.127.249.74 |
frppl.com domain information
2015-12-21 123.60.73.10
2015-07-01 121.127.249.74
jrjfj.com domain information
2015-12-21 123.60.73.8
2015-07-01 121.127.249.74
pjntx.com domain information
2015-12-28 123.60.73.9
2015-07-01 121.127.249.74
yeaqm.com domain information
2015-12-27 123.60.73.6
2015-07-01 121.127.249.74
I quickly check the server HTTP response header and this is what I’ve found that they are all the same:
HTTP/1.1 403 Forbidden
Server: nginx/1.6.2
Date: (current time of check)
Content-Type: text/html
Content-Length: 168
Connection: keep-alive
Okay, we already have 123.60.73.6, 123.60.73.8, 123.60.73.9, 123.60.73.10. Lets just quickly perform the HTTP response header loop for the whole /24 subnet (or maybeee i lil bit more). This is the result:
123.60.73.1
123.60.73.2
123.60.73.3
123.60.73.4
123.60.73.5
123.60.73.6
123.60.73.7
123.60.73.8
123.60.73.9
123.60.73.10
123.60.73.11
123.60.73.12
123.60.73.13
123.60.73.14
123.60.73.15
123.60.73.16
123.60.73.17
123.60.73.18
123.60.73.19
123.60.73.21
123.60.73.22
123.60.73.23
123.60.73.24
123.60.73.25
123.60.73.26
123.60.73.27
123.60.73.28
123.60.73.29
123.60.73.30
123.60.73.31
123.60.73.32
123.60.73.33
123.60.73.34
123.60.73.35
123.60.73.36
123.60.73.37
123.60.73.38
123.60.73.39
123.60.73.40
123.60.73.41
123.60.73.42
123.60.73.43
123.60.73.44
123.60.73.45
123.60.73.46
123.60.73.47
123.60.73.48
123.60.73.49
123.60.73.50
123.60.73.51
123.60.73.52
123.60.73.53
123.60.73.54
123.60.73.55
123.60.73.56
123.60.73.57
123.60.73.58
123.60.73.59
123.60.73.60
123.60.73.61
123.60.74.1
123.60.74.2
123.60.74.3
123.60.74.4
123.60.74.5
123.60.74.6
123.60.74.7
123.60.74.8
123.60.74.9
123.60.74.10
123.60.74.11
123.60.74.12
123.60.74.13
123.60.74.14
123.60.74.15
123.60.74.16
123.60.74.17
123.60.74.18
123.60.74.19
123.60.74.20
123.60.74.21
123.60.74.22
123.60.74.23
123.60.74.24
123.60.74.25
123.60.74.26
123.60.74.27
123.60.74.28
123.60.74.29
123.60.74.30
123.60.74.31
123.60.74.32
123.60.74.33
123.60.74.34
123.60.74.35
123.60.74.36
123.60.74.37
123.60.74.38
123.60.74.39
123.60.74.40
123.60.74.41
123.60.74.42
123.60.74.43
123.60.74.44
123.60.74.45
123.60.74.46
123.60.74.47
123.60.74.48
123.60.74.49
123.60.74.50
123.60.74.51
123.60.74.52
123.60.74.53
123.60.74.54
123.60.74.55
123.60.74.56
123.60.74.57
123.60.74.58
123.60.74.59
123.60.74.60
123.60.74.61 |
123.60.73.1
123.60.73.2
123.60.73.3
123.60.73.4
123.60.73.5
123.60.73.6
123.60.73.7
123.60.73.8
123.60.73.9
123.60.73.10
123.60.73.11
123.60.73.12
123.60.73.13
123.60.73.14
123.60.73.15
123.60.73.16
123.60.73.17
123.60.73.18
123.60.73.19
123.60.73.21
123.60.73.22
123.60.73.23
123.60.73.24
123.60.73.25
123.60.73.26
123.60.73.27
123.60.73.28
123.60.73.29
123.60.73.30
123.60.73.31
123.60.73.32
123.60.73.33
123.60.73.34
123.60.73.35
123.60.73.36
123.60.73.37
123.60.73.38
123.60.73.39
123.60.73.40
123.60.73.41
123.60.73.42
123.60.73.43
123.60.73.44
123.60.73.45
123.60.73.46
123.60.73.47
123.60.73.48
123.60.73.49
123.60.73.50
123.60.73.51
123.60.73.52
123.60.73.53
123.60.73.54
123.60.73.55
123.60.73.56
123.60.73.57
123.60.73.58
123.60.73.59
123.60.73.60
123.60.73.61
123.60.74.1
123.60.74.2
123.60.74.3
123.60.74.4
123.60.74.5
123.60.74.6
123.60.74.7
123.60.74.8
123.60.74.9
123.60.74.10
123.60.74.11
123.60.74.12
123.60.74.13
123.60.74.14
123.60.74.15
123.60.74.16
123.60.74.17
123.60.74.18
123.60.74.19
123.60.74.20
123.60.74.21
123.60.74.22
123.60.74.23
123.60.74.24
123.60.74.25
123.60.74.26
123.60.74.27
123.60.74.28
123.60.74.29
123.60.74.30
123.60.74.31
123.60.74.32
123.60.74.33
123.60.74.34
123.60.74.35
123.60.74.36
123.60.74.37
123.60.74.38
123.60.74.39
123.60.74.40
123.60.74.41
123.60.74.42
123.60.74.43
123.60.74.44
123.60.74.45
123.60.74.46
123.60.74.47
123.60.74.48
123.60.74.49
123.60.74.50
123.60.74.51
123.60.74.52
123.60.74.53
123.60.74.54
123.60.74.55
123.60.74.56
123.60.74.57
123.60.74.58
123.60.74.59
123.60.74.60
123.60.74.61
Okay i’m running out of time, my kids are waiting for me outside.
From my quick check on the domain resolved to the IP range 123.60.73.1 – 123.60.73.61 , I can safely assume that those are APT16 new infra. But I not really confident to attribute 123.60.74.1 – 123.60.74.61, but those IPs in that range, and domains revolved to that range, are fishy!
Happy hunting
Posted: August 28th, 2015 | Author: xanda | Filed under: IT Related | Tags: Angler Exploit Kit | No Comments »
Few friends ping-ed me recently and asked for intel on Angler EK. One of the thing that i can really release publicly at the moment without interfering/conflicting with my employer’s interest, is the yara rule to detect the Angler Exploit Kit redirector. The redirector is actually JS code, injected to innocent page to redirect visitor to Angler Exploit Kit.
Here you go:
rule AnglerEKredirector
{
meta:
description = "Angler Exploit Kit Redirector"
ref = "http://blog.xanda.org/2015/08/28/yara-rule-for-angler-ek-redirector-js/"
author = "adnan.shukor@gmail.com"
date = "08-July-2015"
impact = "5"
version = "1"
strings:
$ekr1 = "<script>var date = new Date(new Date().getTime() + 60*60*24*7*1000);" fullword
$ekr2 = "document.cookie=\"PHP_SESSION_PHP="
$ekr3 = "path=/; expires=\"+date.toUTCString();</script>" fullword
$ekr4 = "<iframe src=" fullword
$ekr5 = "</iframe></div>" fullword
condition:
all of them
} |
rule AnglerEKredirector
{
meta:
description = "Angler Exploit Kit Redirector"
ref = "http://blog.xanda.org/2015/08/28/yara-rule-for-angler-ek-redirector-js/"
author = "adnan.shukor@gmail.com"
date = "08-July-2015"
impact = "5"
version = "1"
strings:
$ekr1 = "<script>var date = new Date(new Date().getTime() + 60*60*24*7*1000);" fullword
$ekr2 = "document.cookie=\"PHP_SESSION_PHP="
$ekr3 = "path=/; expires=\"+date.toUTCString();</script>" fullword
$ekr4 = "<iframe src=" fullword
$ekr5 = "</iframe></div>" fullword
condition:
all of them
}
Posted: June 10th, 2015 | Author: xanda | Filed under: IT Related | 1 Comment »
I’ve recently worked on yara rule to detect jjencode. So here is my simple rule:
rule jjEncode
{
meta:
description = "jjencode detection"
ref = "https://blog.xanda.org/2015/06/10/yara-rule-for-jjencode/"
author = "adnan.shukor@gmail.com"
date = "10-June-2015"
version = "1"
impact = 3
hide = false
strings:
$jjencode = /(\$|[\S]+)=~\[\]\;(\$|[\S]+)\=\{[\_]{3}\:[\+]{2}(\$|[\S]+)\,[\$]{4}\:\(\!\[\]\+["]{2}\)[\S]+/ fullword
condition:
$jjencode
}
See you next time 🙂
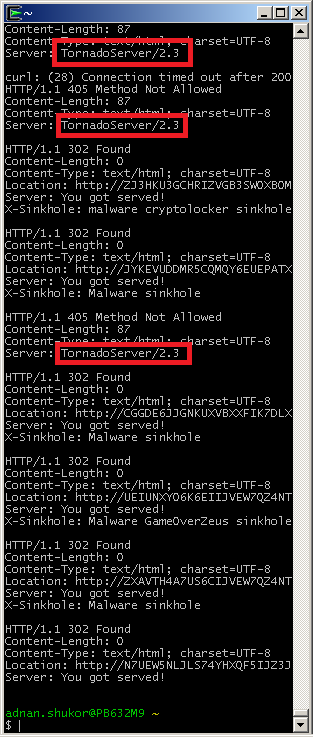
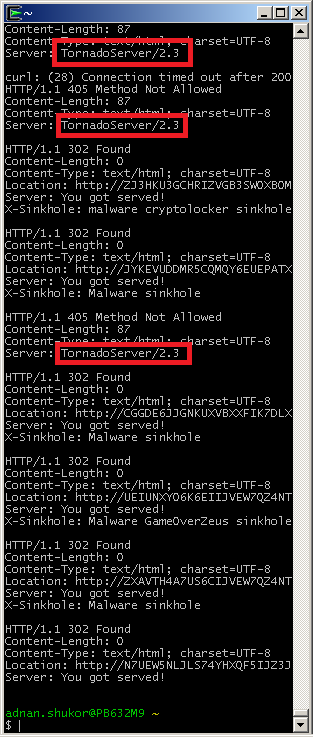
Posted: July 1st, 2014 | Author: xanda | Filed under: IT Related | Tags: sinkhole | No Comments »
A short update, a note for myself
Last May, while discussing with a friend, we’ve concluded that these 2 header (HTTP header) example indicate that those servers are sinkhole servers:
HTTP/1.0 200 OK
Server: Apache 1.0/SinkSoft
Date: Tue, 27 May 2014 06:11:29 GMT
Content-Length: 0
Connection: close |
HTTP/1.0 200 OK
Server: Apache 1.0/SinkSoft
Date: Tue, 27 May 2014 06:11:29 GMT
Content-Length: 0
Connection: close
HTTP/1.1 200 OK
Date: Mon, 26 May 2014 07:26:20 GMT
Server: Apache/2.2.20 (Ubuntu)
X-Sinkhole: malware-sinkhole
Vary: Accept-Encoding
Content-Length: 0
Content-Type: text/html |
HTTP/1.1 200 OK
Date: Mon, 26 May 2014 07:26:20 GMT
Server: Apache/2.2.20 (Ubuntu)
X-Sinkhole: malware-sinkhole
Vary: Accept-Encoding
Content-Length: 0
Content-Type: text/html
So we can look for:
- Apache 1.0/SinkSoft
- X-Sinkhole:
Today, I’ve found “Server: TornadoServer” is another indicator. But i’m not yet 100% sure. Comments are welcome