Internet Explorer CMshtmlEd::Exec() 0day
Posted: September 17th, 2012 | Author: xanda | Filed under: IT Related | 3 Comments »As discussed [1] [2] [3] in Twitter couple of hours ago,without any delay, Metasploit team did very well in their part to release the working version of the exploit and port it to their framework. Awesome work guys! Some workarounds are available in MyCERT’s writeup
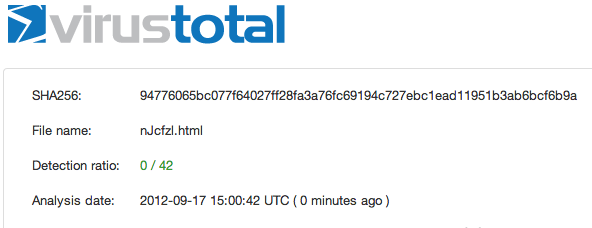
$ yara -r newIE0daymshtmlExec.yar /tmp/0dayIE/ newIE0daymshtmlExec /tmp/0dayIE//CVE-IE8 0day/2a2e2efffa382663ba10c492f407dda8a686a777858692d073712d1cc9c5f265_Protect.html newIE0daymshtmlExec /tmp/0dayIE//CVE-IE8 0day/9d66323794d493a1deaab66e36d36a820d814ee4dd50d64cddf039c2a06463a5_exploit.html newIE0daymshtmlExec /tmp/0dayIE//Niuya.html newIE0daymshtmlExec /tmp/0dayIE//nJcfzl.html |
And.. I’m ready with the detection “rule” and as mention in previous entry, it will only be share with several private group. If you need to get the feeds, kindly drop me an email at adnan.shukor @ G!
Thanks
Reference:
- http://eromang.zataz.com/2012/09/16/zero-day-season-is-really-not-over-yet/
- http://blog.vulnhunt.com/index.php/2012/09/17/ie-execcommand-fuction-use-after-free-vulnerability-0day/
- http://labs.alienvault.com/labs/index.php/2012/new-internet-explorer-zero-day-being-exploited-in-the-wild/
- http://www.mycert.org.my/en/services/advisories/mycert/2012/main/detail/908/index.html
Updated
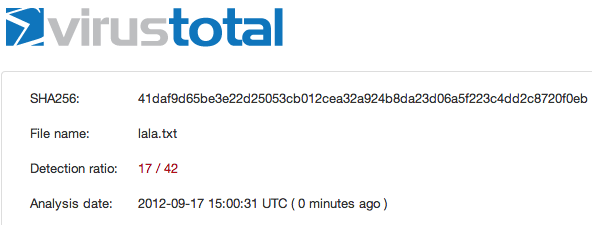
Metasploit detection rate:
[…] done a quick writeup on this news earlier, and back then, there is no patch/fixit yet released by Microsoft. So I end up […]
Metasploit has release an exploit module “ie_execcommand_uaf“ and this module is working for IE 7/8/9 on XP/Vista/7.
yes, that is what has been mentioned in my post 🙂