RedKit Patterns – Additional Info to @fknsec Writeup
Posted: December 12th, 2012 | Author: xanda | Filed under: IT Related | Tags: Exploit Kit, pattern, redkit, regex | 4 Comments »It’s been a while since the last time I logged in into my WordPress. I’ve jumped on BlueCoat System‘s bandwagon (and left MyCERT earlier), so I’ve to spent some time to make myself familiar with this new environment and job 🙂
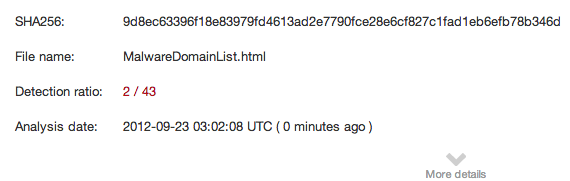
Last week, @fknsec, in his blog, wrote a very good article about RedKit Exploit Kit. But here I would like to add few more interesting facts on the RedKit patterns
- @fknsec did mention about “/hmiq.htm” in his blog, but from my observation, beside Porche and Ferari, the RedKit author also like the letter H. The naming convention for the HTML file will always start from H and ended with .htm (everything in small case). So a working regex for this pattern world be:
/\/h(m|f)[a-z]{2}\.htm$/** updated on 14 Feb 2013 **
Look like this portion is no longer valid at the moment. You can replace it with:/\/[a-z]{4}\.html?$/ - 887.jar and 332.jar is quite unique to RedKit. Go hunt them!
/\/(887|332)\.jar$/
- Same goes to 987.pdf
/\/987.pdf$/
- c.htm as mentioned by @fknsec can be in 1 char (letter) file name (in small case), or it can also be in 2 digit (number) and ended with .htm.
/\/([a-z]{1}|\d{2})\.htm$/ - Unlike BlackHole and Cool exploit kit, RedKit will usually be hosted on compromised websites and not having his own special subdomain. Most of the time, RedKit files will be in the main directory of a website/domain
eg: google.com/332.jar
- From my observation, among the famous tricks to lure victim to RedKit are:
- Redirector script planted in jquery JS file
- Redirector in “Domain to sell” placeholder
I think that’s all for today. I don’t know when is the next time to update my blog, since will keep my self busy in these coming weeks, with my first baby is going to execute /h(is|er)/ first version of “Hello World” script in near soon.
Till then, stay safe everyone & happy hunting!
Reference:
- http://fortknoxnetworks.blogspot.com/2012/12/exploit-medfos-url-detection-with-drop.html
- http://malware.dontneedcoffee.com/2012/08/cve-2012-4681-redkit-exploit-kit-i-want.html